Search.hideyoursearch.win browser hijacker – why is it an unreliable program?
As soon as Search.hideyoursearch.win enters your operating system it will make a few fundamental changes to your default web browser’s settings. In fact, quite a few users think that this application is a malicious infection similar to browser hijackers. Our specialists say it could be that the software might show third-party advertisements while the user browses and its developers may generate advertising revenue when he clicks them. Although it actually looks like any other regular search engine, you should not fall for this trick. The problem is that no one takes responsibility for Search.hideyoursearch.win redirects and the content of the websites that you may be forced to visit. Secondly, you may be tricked into downloading useless software to your PC system, which may lead you to unwanted pop-up ads, in-text links, banners and similar unwanted things.
Our research specialists say that Search.hideyoursearch.win is developed by Bontio, Inc., and it usually comes with an update for Pokki Windows 8 Start Menu. In the middle, of course, there is a search dialog box. According to this program’s Privacy Policy, it shares gathered data with third-parties “for the purpose of developing or delivering advertising.” Therefore, do not be surprised if this controversial program starts sending you intrusive pop-up or banner ads. As soon as it gets inside, it alters some of PC’s parameters, including default search engine and homepage without user’s consent. To avoid this happening, you have to be careful when installing freewares on your computer since this misleading plug-in tends to spread as an additional component alongside various download managers, PDF creators, media players and so on. Although this hijacker redirects to search.yahoo.com, it does not mean that you are shown reliable search results.
When did the PUP attack my computer?
Fortunately, They also notice that Search.hideyoursearch.win has changed their default search engine to ask.com. You should know that these ads may not even look like normal ads so you may not even know that you actually click on an unsafe ad. Most of the Internet is chock full of parasites like this, marching around without any decency. All these features of Search.hideyoursearch.win virus ambush people and are not that easy to flee from. manual removal guide to assist you – scroll down below this article and take a look at our step-by-step Also, keep away from downloading unreliable or illegal software from unreputable download sites.
As regards the removal of Search.hideyoursearch.win, we recommend that you implement a reputable security program. This is crucial since an incomplete removal due to a missed or skipped step could have unwanted outcomes, to say the least. You had to make some errors to receive this pest. We advise you to replace it with a well-known and leading search engine, for instance, Bing, Yahoo, or Google. Consequently, you receive such personalized offers.
How to remove this Conduit Toolbar?
You might begin to notice the activity of Search.hideyoursearch.win virus Some of the websites may collect your information for online marketing purposes. Unfortunately, most of the users fail to realize the importance of the installation settings, so they often just leave the automatically marked “default/standard” button and proceed to the next installation step. We provide instructions for that right below this description. Then Instead, we recommend choosing Advanced or Custom mode – these options allow you to opt-out the optional software components. Use these scanners for regular checkups and be always aware of the condition of your PC. This is paramount since these extra programs are typically PUPs (potentially unwanted programs) such as Search.hideyoursearch.win is.
Search.hideyoursearch.win Behavior
- Integrates into the web browser via the Search.hideyoursearch.win browser extension
- Search.hideyoursearch.win Connects to the internet without your permission
- Modifies Desktop and Browser Settings.
- Redirect your browser to infected pages.
- Slows internet connection
- Changes user's homepage
- Shows Fake Security Alerts, Pop-ups and Ads.
- Distributes itself through pay-per-install or is bundled with third-party software.
- Installs itself without permissions
- Search.hideyoursearch.win Deactivates Installed Security Software.
- Steals or uses your Confidential Data
- Common Search.hideyoursearch.win behavior and some other text emplaining som info related to behavior
Search.hideyoursearch.win effected Windows OS versions
- Windows 8
- Windows 7
- Windows Vista
- Windows XP
Warning, multiple anti-virus scanners have detected possible malware in Search.hideyoursearch.win.
| Anti-Virus Software | Version | Detection |
|---|---|---|
| NANO AntiVirus | 0.26.0.55366 | Trojan.Win32.Searcher.bpjlwd |
| VIPRE Antivirus | 22224 | MalSign.Generic |
| ESET-NOD32 | 8894 | Win32/Wajam.A |
| McAfee-GW-Edition | 2013 | Win32.Application.OptimizerPro.E |
| Dr.Web | Adware.Searcher.2467 | |
| McAfee | 5.600.0.1067 | Win32.Application.OptimizerPro.E |
| Kingsoft AntiVirus | 2013.4.9.267 | Win32.Troj.Generic.a.(kcloud) |
| Tencent | 1.0.0.1 | Win32.Trojan.Bprotector.Wlfh |
| Qihoo-360 | 1.0.0.1015 | Win32/Virus.RiskTool.825 |
| VIPRE Antivirus | 22702 | Wajam (fs) |
| K7 AntiVirus | 9.179.12403 | Unwanted-Program ( 00454f261 ) |
| Baidu-International | 3.5.1.41473 | Trojan.Win32.Agent.peo |
Search.hideyoursearch.win Geography
Remove Search.hideyoursearch.win from Windows
Remove Search.hideyoursearch.win from Windows XP:
- Drag mouse cursor to the left of the Task Bar and click Start to open a menu.
- Open the Control Panel and double-click Add or Remove Programs.
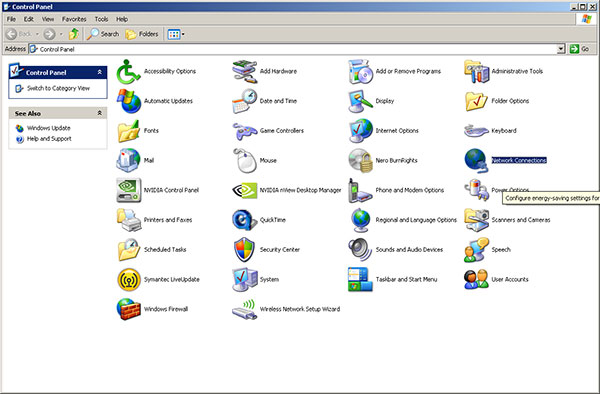
- Remove the undesirable application.
Remove Search.hideyoursearch.win from Windows Vista or Windows 7:
- Click the Start menu icon on the Task Bar and select Control Panel.
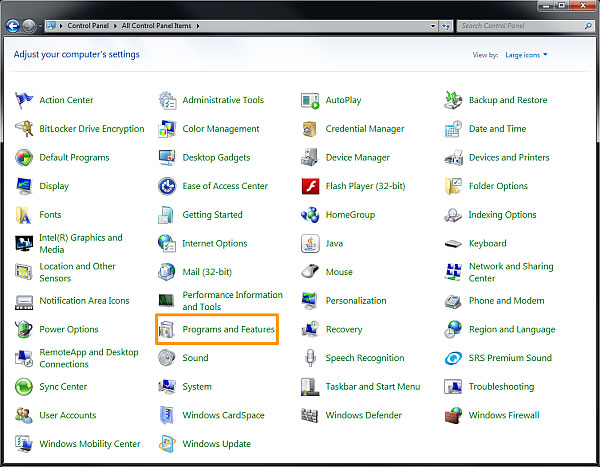
- Select Uninstall a program and locate the undesirable application
- Right-click the application you want to delete and select Uninstall.
Remove Search.hideyoursearch.win from Windows 8:
- Right-click on the Metro UI screen, select All apps and then Control Panel.

- Go to Uninstall a program and right-click the application you want to delete.
- Select Uninstall.
Remove Search.hideyoursearch.win from Your Browsers
Remove Search.hideyoursearch.win from Internet Explorer
- Go for Alt+T and click on Internet Options.
- In this section, move to the 'Advanced' tab and then click on the 'Reset' button.
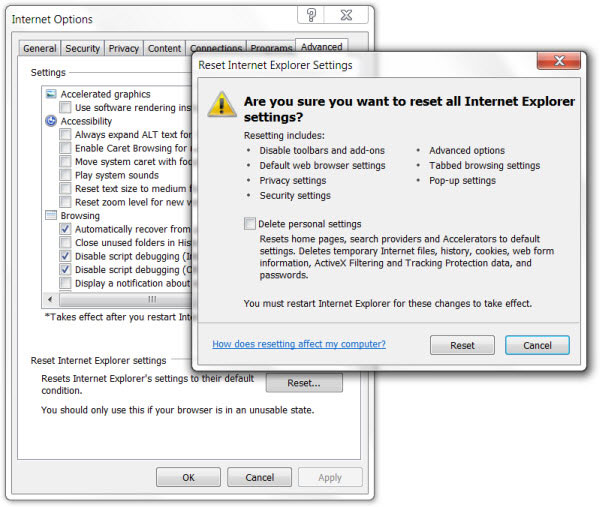
- Navigate to the 'Reset Internet Explorer settings' → then to 'Delete personal settings' and press on 'Reset' option.
- After this, click on 'Close' and go for OK to have modifications saved.
- Click on the tabs Alt+T and go for Manage Add-ons. Move to Toolbars and Extensions and here, get rid of the unwanted extensions.
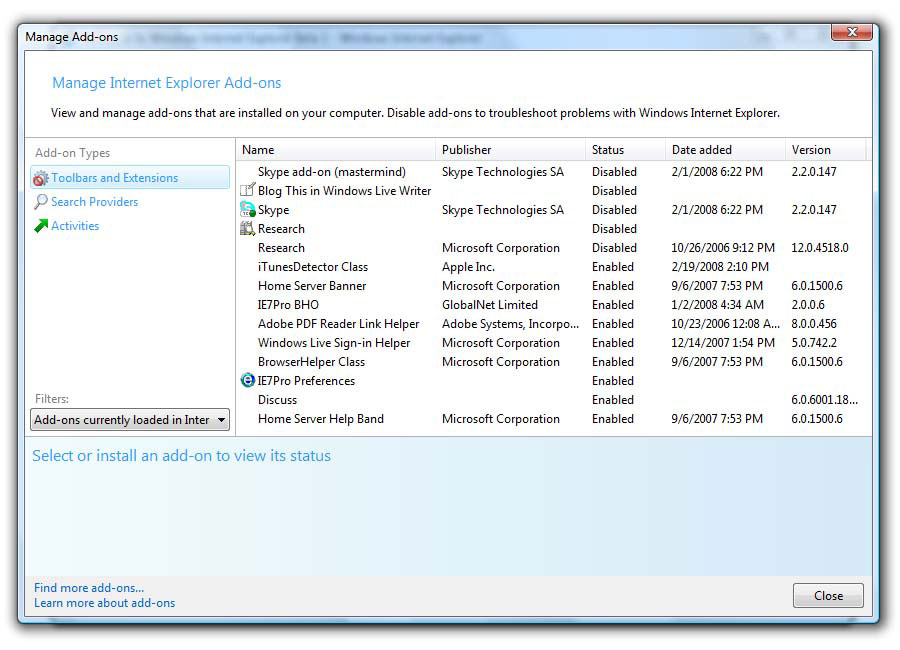
- Click on Search Providers and set any page as your new search tool.
Delete Search.hideyoursearch.win from Mozilla Firefox
- As you have your browser opened, type in about:addons in the shown URL field.
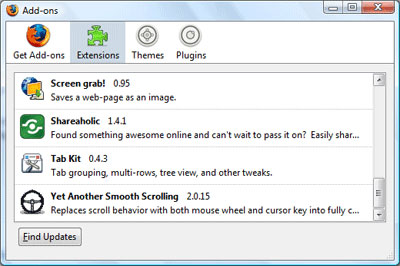
- Move through Extensions and Addons list, delete the items having something in common with Search.hideyoursearch.win (or those which you may find unfamiliar). If the extension is not provided by Mozilla, Google, Microsoft, Oracle or Adobe, you should be almost sure you have to erase it.
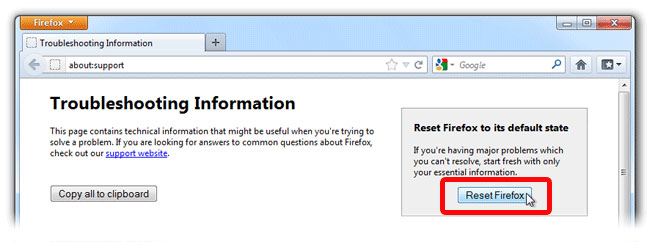
- Then, reset Firefox by doing this: move to Firefox ->Help (Help in menu for OSX users) -> Troubleshooting Information. Finally,Reset Firefox.
Terminate Search.hideyoursearch.win from Chrome
- In the displayed URL field, type in chrome://extensions.
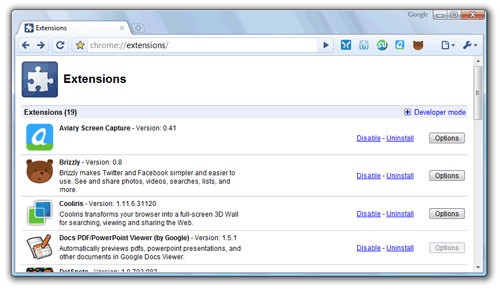
- Take a look at the provided extensions and take care of those which you find unnecessary (those related to Search.hideyoursearch.win) by deleting it. If you do not know whether one or another must be deleted once and for all, disable some of them temporarily.
- Then, restart Chrome.
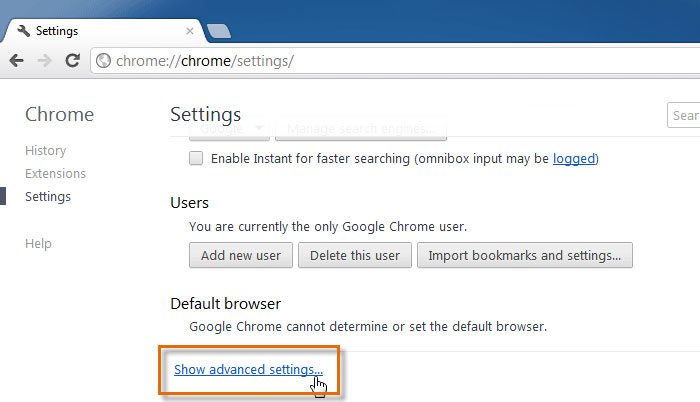
- Optionally, you may type in chrome://settings in URL bar, move to Advanced settings, navigate to the bottom and choose Reset browser settings.