HOW CAN I GET INFECTED WITH RECO ransomwareΔ. virus?
Polícia Judiciária RECO ransomware relies on trojan horse when it needs to enter its target PC system without a sign. virus) is a Germain ransomware infection from Ukash virus group. Sometimes this alert is titled: cyber criminals offer special decoding software. It sneaks into your computer stealthily, looks around for data to be damaged, exploits malicious script to encrypt it and drops you a message embracing the ransom note. Most of them do not download the product themselves, as it is noticed that Zlob is used again for this malicious purposes. It reports many infections found on a system and offers purchasing full version of the software.
The most typical method, which is used by RECO ransomware The payload of this variant is expected to be downloaded by poor Internet users. The files cannot be unlocked using the same key. Never trust this message. Here’s what this ransomware virus claims once it gets inside the system: Below we provide the message that appeared on the screen of computer that was infected in New York:
What are the most typical ways this malware infects computers?
There is no one set technique using which, the CryptMix virus can enter your computer. Although the message looks very real it has nothing to do with Autoren Komponisten Musikverleger So soon you may not even be able to recover your files from a backup. If you can’t get on the Internet, try to run a scan when on Safe Mode with Networking. You should try avoiding these infections and if your computer gets attacked, never follow their instructions.
This virus is mostly spread via fake e-mails, so you should NEVER open letters from unknown senders or download attachments from such letters. Depending on the version of RECO ransomware and the severity of infection there are several ways. Thus, you can check your device via settings menu to see if any questionable applications have those privileges turned on. For prevention keep backups in external storage devices. Terminating them before they are activated might also save you trouble from dealing with ransomware later. Moreover, police would never inform about the fines that you have to pay by remotely locking your computer.
Remove RECO ransomware ransomware and decrypt your files
* Users infected with If not, utilize services like Microsoft OneDrive or Google Disk to recover some of your files. If the virus blocks it, select Save Mode with Networking. However, right after you fix your computer, start to think how to prevent data loss in the future. www.2remove-threats.com/download. People that are reading this article simply for pure awareness should store their files in backup storages, USB flash drives. R-studio
RECO ransomware Behavior
- Shows Fake Security Alerts, Pop-ups and Ads.
- Steals or uses your Confidential Data
- Integrates into the web browser via the RECO ransomware browser extension
- RECO ransomware Shows commercial adverts
- Redirect your browser to infected pages.
- Modifies Desktop and Browser Settings.
- Installs itself without permissions
- RECO ransomware Connects to the internet without your permission
- Changes user's homepage
- Common RECO ransomware behavior and some other text emplaining som info related to behavior
- RECO ransomware Deactivates Installed Security Software.
RECO ransomware effected Windows OS versions
- Windows 8
- Windows 7
- Windows Vista
- Windows XP
Warning, multiple anti-virus scanners have detected possible malware in RECO ransomware.
| Anti-Virus Software | Version | Detection |
|---|---|---|
| VIPRE Antivirus | 22702 | Wajam (fs) |
| Malwarebytes | v2013.10.29.10 | PUP.Optional.MalSign.Generic |
| Kingsoft AntiVirus | 2013.4.9.267 | Win32.Troj.Generic.a.(kcloud) |
| K7 AntiVirus | 9.179.12403 | Unwanted-Program ( 00454f261 ) |
| Qihoo-360 | 1.0.0.1015 | Win32/Virus.RiskTool.825 |
| VIPRE Antivirus | 22224 | MalSign.Generic |
| Malwarebytes | 1.75.0.1 | PUP.Optional.Wajam.A |
| Dr.Web | Adware.Searcher.2467 | |
| ESET-NOD32 | 8894 | Win32/Wajam.A |
| McAfee | 5.600.0.1067 | Win32.Application.OptimizerPro.E |
RECO ransomware Geography
Remove RECO ransomware from Windows
Remove RECO ransomware from Windows XP:
- Drag mouse cursor to the left of the Task Bar and click Start to open a menu.
- Open the Control Panel and double-click Add or Remove Programs.
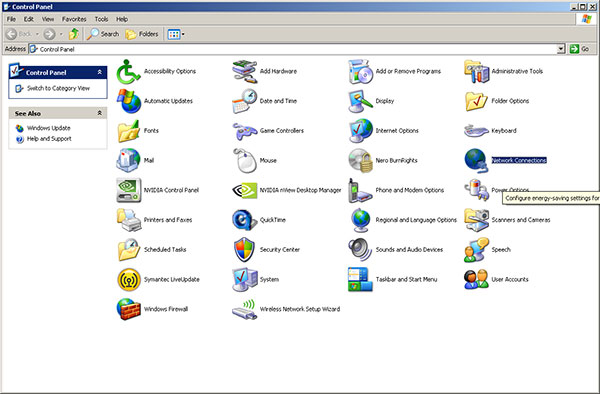
- Remove the undesirable application.
Remove RECO ransomware from Windows Vista or Windows 7:
- Click the Start menu icon on the Task Bar and select Control Panel.
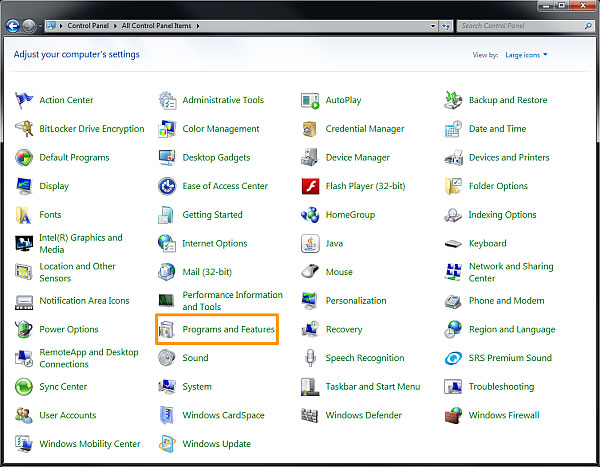
- Select Uninstall a program and locate the undesirable application
- Right-click the application you want to delete and select Uninstall.
Remove RECO ransomware from Windows 8:
- Right-click on the Metro UI screen, select All apps and then Control Panel.

- Go to Uninstall a program and right-click the application you want to delete.
- Select Uninstall.
Remove RECO ransomware from Your Browsers
Remove RECO ransomware from Internet Explorer
- Go for Alt+T and click on Internet Options.
- In this section, move to the 'Advanced' tab and then click on the 'Reset' button.
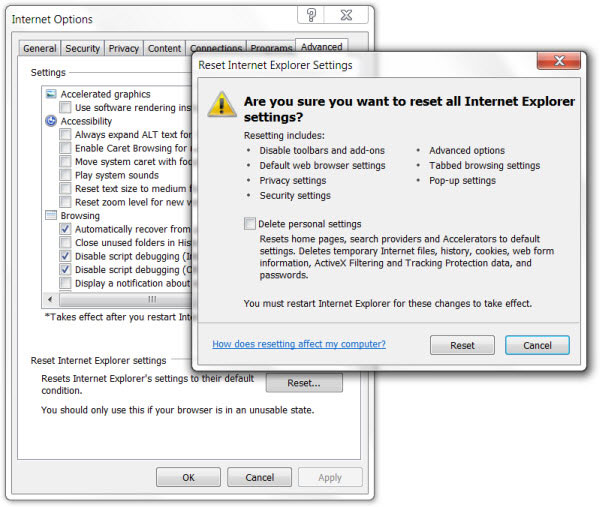
- Navigate to the 'Reset Internet Explorer settings' → then to 'Delete personal settings' and press on 'Reset' option.
- After this, click on 'Close' and go for OK to have modifications saved.
- Click on the tabs Alt+T and go for Manage Add-ons. Move to Toolbars and Extensions and here, get rid of the unwanted extensions.
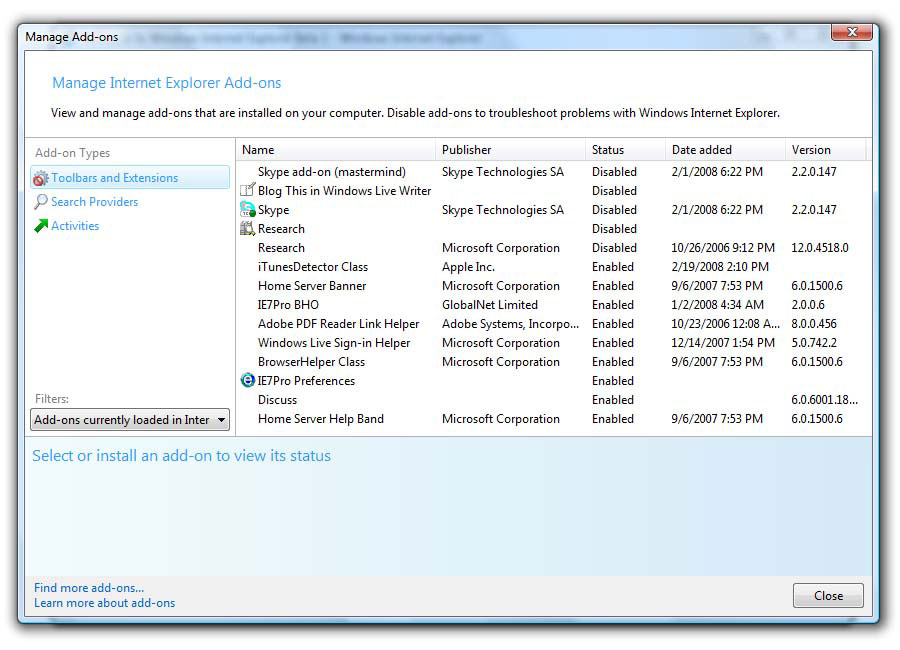
- Click on Search Providers and set any page as your new search tool.
Delete RECO ransomware from Mozilla Firefox
- As you have your browser opened, type in about:addons in the shown URL field.
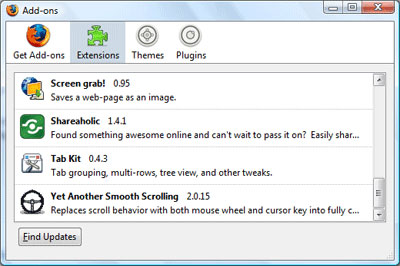
- Move through Extensions and Addons list, delete the items having something in common with RECO ransomware (or those which you may find unfamiliar). If the extension is not provided by Mozilla, Google, Microsoft, Oracle or Adobe, you should be almost sure you have to erase it.
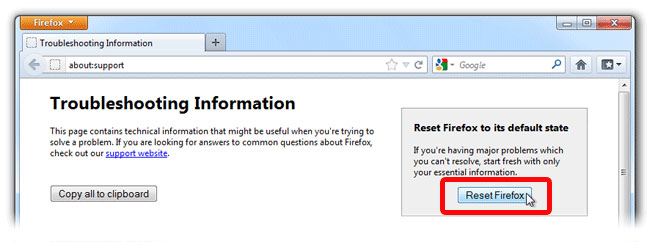
- Then, reset Firefox by doing this: move to Firefox ->Help (Help in menu for OSX users) -> Troubleshooting Information. Finally,Reset Firefox.
Terminate RECO ransomware from Chrome
- In the displayed URL field, type in chrome://extensions.
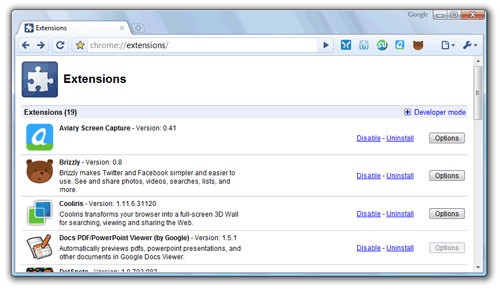
- Take a look at the provided extensions and take care of those which you find unnecessary (those related to RECO ransomware) by deleting it. If you do not know whether one or another must be deleted once and for all, disable some of them temporarily.
- Then, restart Chrome.
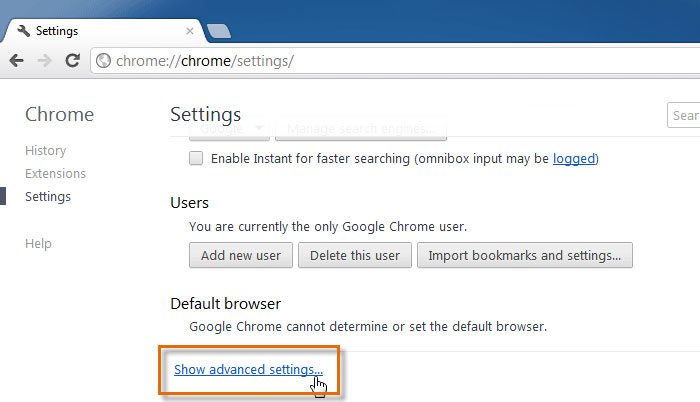
- Optionally, you may type in chrome://settings in URL bar, move to Advanced settings, navigate to the bottom and choose Reset browser settings.