How can I install Brazzerssurvey.com on my computer?
Since Brazzerssurvey.com is an ordinary adware, its infiltration method is predictable. That’s why it has been categorized as a potentially unwanted program (also known as adware). For the most part, this program enters your system to deliver commercial content and make some money out of it. flood its victim with advertisements and Instead of that, we would like to recommend thinking twice before downloading such programs to your computer and minimizing all the risk to the minimum. However, malware studies have revealed that such and similar programs have hidden traits and usually appear to be more than useless.
By the way, we haven’t mentioned yet that this add-on This method can’t be imagined without freeware and shareware that is usually packed with ‘optional’ downloads for monetization. or not because usually advertisements displayed by this malware are labeled with a slogan “Ads by Brazzerssurvey.com” or “Brought to you by Brazzerssurvey.com”. In this article we will provide you with detailed instructions how to eliminate this infection either manually or automatically so it’s completely up to you which method to choose. Typically, it should appear on one of program’s installation windows. Some download websites may have it bundled to the main installer of the programs.
How can Brazzerssurvey.com Lightly hijack my computer?
Brazzerssurvey.com features various similarities to Google Chrome, even the color scheme is very similar. develops Brazzerssurvey.com. manually. You will find a full guide how to do it at the end of this article. Crooks very frequently pretend to be concerned Microsoft programmers, making sure that computer systems are running smoothly. For that we recommend choosing only Custom or Advanced installation process and deselecting all check marks that say that you agree to install add-ons, plugins,
We suggest you follow the manual removal instructions below and then click the represented button to install a reliable Windows security application which could remove files responsible for the unauthorized connection to the remote servers automatically. They come bundled with the latter. The most important thing is to choose secure installation settings – so opt for “advanced” or “custom” mode. It is very important to have a latest version of a security tool, so the scan is effective. Hopefully, you do not need to waste your time eliminating third-party malware, but, if you do, we recommend using automated malware removal software for the quickest and most efficient results. careful during the installation. That is why we suggest that you should use a reliable antimalware program.
Is there a way to remove Brazzerssurvey.com?
It works as browser add-on that can be added to all most common web browsers, including Mozilla Firefox, Google Chrome, Internet Explorer or even Safari. It records clicks, impressions, search terms, browsing history, browser settings, browser language, and some other non-personally identifiable information. Press on the button below to download a 100% reliable tool which would diagnose the condition of your computer. Even though it’s not a dangerous virus itself, it can lead you to some more severe cyber security infections, therefore it needs to be removed as soon as possible. Scanning with anti-malware tools and direct uninstall should handle IE advertisements. Lastly, it is wise to take a look at the privacy policy provisions of the application you are about to install. An anti-spyware program easily tracks the adware and all its related potentially malicious files and deletes them.
Brazzerssurvey.com Behavior
- Integrates into the web browser via the Brazzerssurvey.com browser extension
- Distributes itself through pay-per-install or is bundled with third-party software.
- Changes user's homepage
- Brazzerssurvey.com Connects to the internet without your permission
- Modifies Desktop and Browser Settings.
- Shows Fake Security Alerts, Pop-ups and Ads.
- Redirect your browser to infected pages.
- Steals or uses your Confidential Data
- Brazzerssurvey.com Deactivates Installed Security Software.
- Slows internet connection
- Common Brazzerssurvey.com behavior and some other text emplaining som info related to behavior
- Installs itself without permissions
Brazzerssurvey.com effected Windows OS versions
- Windows 8
- Windows 7
- Windows Vista
- Windows XP
Warning, multiple anti-virus scanners have detected possible malware in Brazzerssurvey.com.
| Anti-Virus Software | Version | Detection |
|---|---|---|
| Qihoo-360 | 1.0.0.1015 | Win32/Virus.RiskTool.825 |
| ESET-NOD32 | 8894 | Win32/Wajam.A |
| VIPRE Antivirus | 22702 | Wajam (fs) |
| Baidu-International | 3.5.1.41473 | Trojan.Win32.Agent.peo |
| Kingsoft AntiVirus | 2013.4.9.267 | Win32.Troj.Generic.a.(kcloud) |
| Dr.Web | Adware.Searcher.2467 | |
| McAfee-GW-Edition | 2013 | Win32.Application.OptimizerPro.E |
| Tencent | 1.0.0.1 | Win32.Trojan.Bprotector.Wlfh |
| K7 AntiVirus | 9.179.12403 | Unwanted-Program ( 00454f261 ) |
| Malwarebytes | v2013.10.29.10 | PUP.Optional.MalSign.Generic |
Brazzerssurvey.com Geography
Remove Brazzerssurvey.com from Windows
Remove Brazzerssurvey.com from Windows XP:
- Drag mouse cursor to the left of the Task Bar and click Start to open a menu.
- Open the Control Panel and double-click Add or Remove Programs.
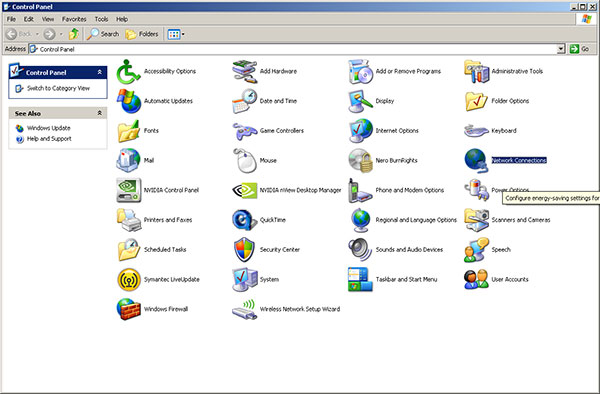
- Remove the undesirable application.
Remove Brazzerssurvey.com from Windows Vista or Windows 7:
- Click the Start menu icon on the Task Bar and select Control Panel.
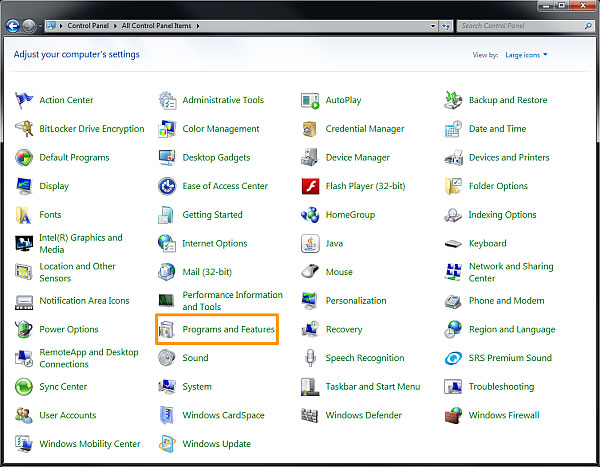
- Select Uninstall a program and locate the undesirable application
- Right-click the application you want to delete and select Uninstall.
Remove Brazzerssurvey.com from Windows 8:
- Right-click on the Metro UI screen, select All apps and then Control Panel.

- Go to Uninstall a program and right-click the application you want to delete.
- Select Uninstall.
Remove Brazzerssurvey.com from Your Browsers
Remove Brazzerssurvey.com from Internet Explorer
- Go for Alt+T and click on Internet Options.
- In this section, move to the 'Advanced' tab and then click on the 'Reset' button.
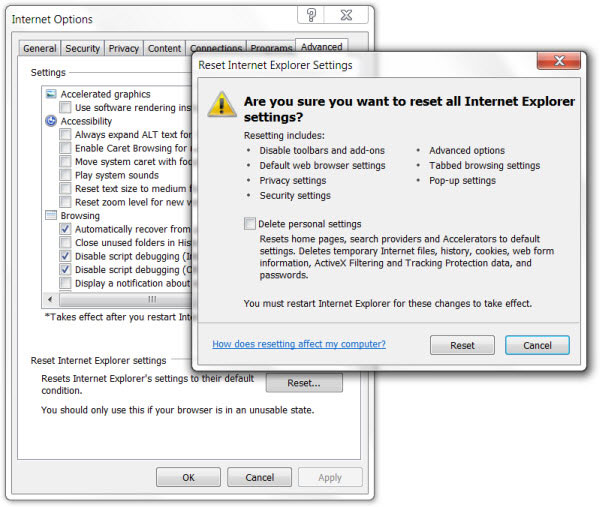
- Navigate to the 'Reset Internet Explorer settings' → then to 'Delete personal settings' and press on 'Reset' option.
- After this, click on 'Close' and go for OK to have modifications saved.
- Click on the tabs Alt+T and go for Manage Add-ons. Move to Toolbars and Extensions and here, get rid of the unwanted extensions.
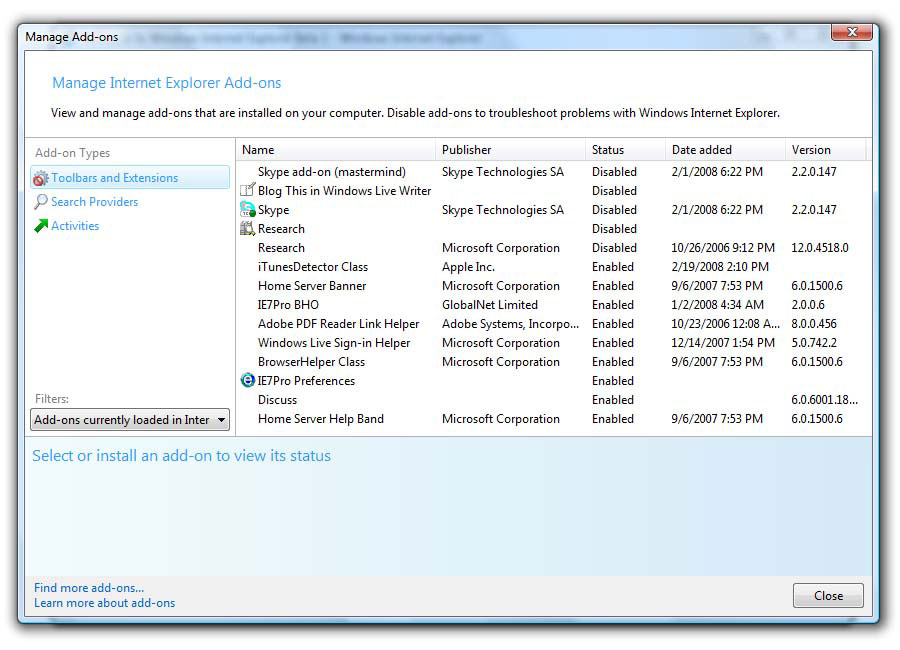
- Click on Search Providers and set any page as your new search tool.
Delete Brazzerssurvey.com from Mozilla Firefox
- As you have your browser opened, type in about:addons in the shown URL field.
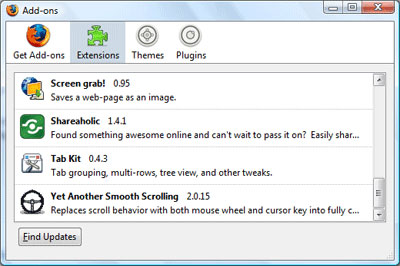
- Move through Extensions and Addons list, delete the items having something in common with Brazzerssurvey.com (or those which you may find unfamiliar). If the extension is not provided by Mozilla, Google, Microsoft, Oracle or Adobe, you should be almost sure you have to erase it.
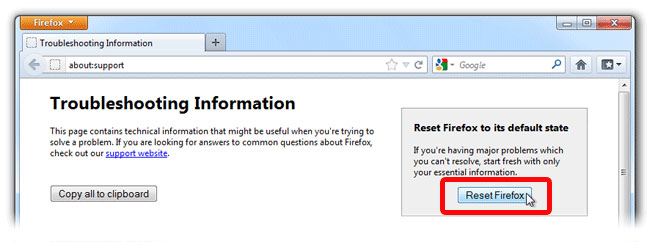
- Then, reset Firefox by doing this: move to Firefox ->Help (Help in menu for OSX users) -> Troubleshooting Information. Finally,Reset Firefox.
Terminate Brazzerssurvey.com from Chrome
- In the displayed URL field, type in chrome://extensions.
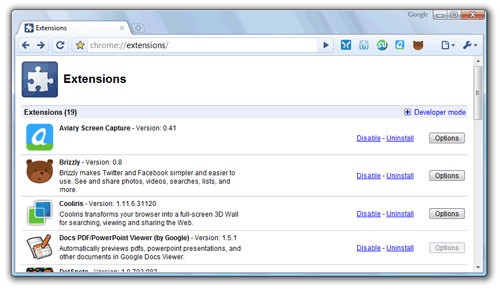
- Take a look at the provided extensions and take care of those which you find unnecessary (those related to Brazzerssurvey.com) by deleting it. If you do not know whether one or another must be deleted once and for all, disable some of them temporarily.
- Then, restart Chrome.
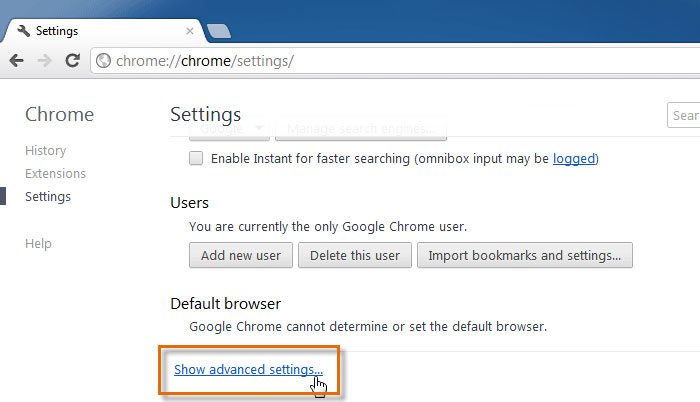
- Optionally, you may type in chrome://settings in URL bar, move to Advanced settings, navigate to the bottom and choose Reset browser settings.